When Load Balancing SharePoint Web Servers and Office Web Apps Servers, some organization would like to adopt SSL offload to improve overall network performance. In these organizations, either the communication between the load balancer and SharePoint Servers are closed so no one could possibly listen in, or just that internal regulations allow non-encrypted traffic between the load balancer and the server behind it. They could bind the SSL certificate only at the load balancer, while on the servers behind, port 80 or other ports are used but without SSL.
In the context of a SharePoint Farm, to support this setup, there are certain configurations to be done on SharePoint as well as the Office Web Apps Server farm (provided that there are more than one OWA servers.
Office Web Apps Server Farm
Configure the Office Web Apps farm with the –AllowHTTP and –SSLOffloaded options set to true.
For example, when creating a new Office Web Apps farm with the cmdlet New-OfficeWebAppsFarm, use the parameter –SSLOffloaded. In this case, the value of –AllowHTTP will be set to true automatically. If the server farm has been created without supporting SSL offload, you could simply, use the Set-OfficeWebAppsFarm cmdlet to change the values.
SharePoint Farm
First of all, there is a difference between path-based site collections and host-named site collections.
For path-based site collections:
Configure Alternative Access Mapping to support the SSL Offload.
When SSL is offloaded to the load balancer, the web applications would not be configured to use SSL. However, there is a difference between the URL that users use to access the web application and the URL set at IIS. For example, the URL used by uses is https://sharepoint.contoso.com as SSL is configured at the load balancer, while in SharePoint, the web applications are created as http://sharepoint.contoso.com. Without AAM accommodating the difference between the internal and external URL, the SharePoint sites may not work properly. One possible behavior is that the browser will warn you that the content is not secure.
To configure AAM to support SSL offload, you should first make sure the public url is set to https:// and then add an internal URL as http://. Simply adding a URL for HTTPS will not work. Here is one way to configure it:
- From SharePoint Central Administration navigation pane, click Application Management.
- In the main pane, under Web Applications, click Configure alternate access mappings.
- From the Internal URL list, click the Internal URL corresponding to the Public URL you want to be accessible through the load balancer.
- The Edit Internal URLs page opens.
- In the URL protocol, host and port box, change the protocol from http:// to https://.

- Click the OK button. You return to the Alternate Access Mappings page.
- On the Menu bar, click Add Internal URLs.
- In the URL protocol, host and port box, type the same internal URL used in step 4, but use the http:// protocol. This allows access to the non-SSL site from behind the load balancer.

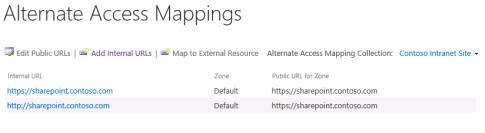
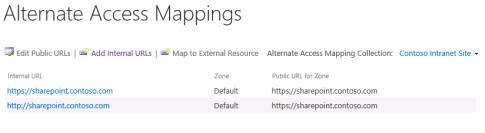
- Click Save. The result should look like this:
For host-named site collections:
AAM does not work. You need to configure the load balancer (or the reverse proxy) to add http header. More specific information can be found in this TechNet article: https://technet.microsoft.com/en-us/library/cc424952.aspx#section2g
If you are using F5 load balancer, you can also find a specific user guide for this scenarios for SharePoint: https://www.f5.com/pdf/deployment-guides/microsoft-sharepoint-2016-dg.pdf